Key Takeaways
- Understand the role and importance of Cloud Access Security Brokers (CASB) in today’s cybersecurity landscape.
- Learn about the various features and benefits CASB offers to organizations.
- Explore real-life applications and the advantages of implementing CASB solutions.
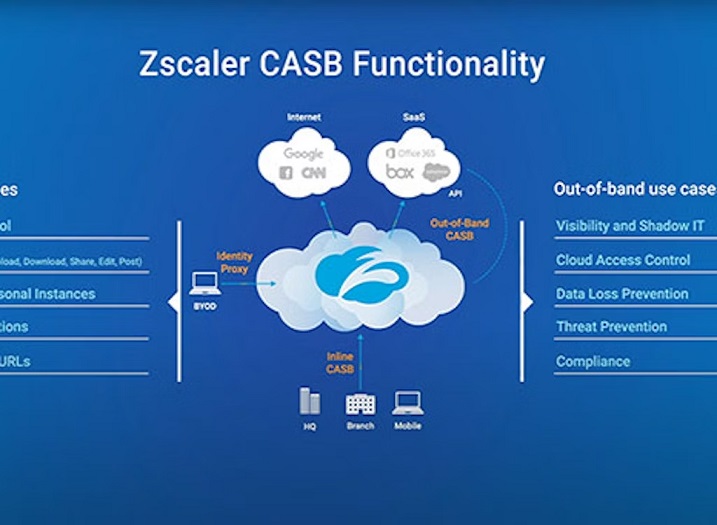
Cloud Access Security Brokers (CASBs) play a pivotal role in modern cybersecurity by securing the intersection of cloud services and enterprise networks. They provide critical visibility into cloud usage, enforce security policies, and manage access controls to protect sensitive data. CASBs also ensure compliance with industry regulations by monitoring data transfers and encrypting information in transit and at rest. By integrating threat protection and data loss prevention (DLP) capabilities, CASBs mitigate risks associated with cloud adoption, making them essential for safeguarding modern digital environments.
What Are Cloud Access Security Brokers?
Cloud Access Security Brokers (CASB) are crucial in helping organizations secure their cloud environments. To guarantee that security regulations are correctly implemented, a CASB acts as a go-between for customers and cloud service providers. These brokers provide oversight and control to manage security risks and maintain compliance in cloud environments. They serve as gatekeepers, monitoring all traffic between the enterprise’s on-premises infrastructure and cloud provider to apply enterprise security policies.
The increasing use of cloud services has made CASBs more critical than ever. Since many businesses struggle to balance security and usability, CASBs are crucial to any cybersecurity plan. Cloud computing has brought up several security difficulties, which CASBs efficiently assist in addressing. These challenges include data breaches, illegal access, and compliance issues.
Benefits of Using CASB
Implementing CASB can provide numerous advantages for organizations. Firstly, CASB solutions offer enhanced visibility into cloud usage, helping to identify potential security risks. Visibility is crucial for understanding how data flows within cloud services and ensuring that all actions comply with corporate policies. Without CASB, organizations often face blind spots in their security postures, leading to vulnerabilities.
Additionally, CASB improves data security by enforcing policies that protect sensitive information. By monitoring data transfers and access points, CASB solutions help to prevent data breaches and unauthorized access. This level of control is indispensable for organizations handling sensitive customer data and intellectual property. For example, CASBs can prevent malicious insiders from exfiltrating sensitive data or block malware from compromising cloud applications.
Key Features of CASB
- Data Loss Prevention (DLP): By enforcing data loss prevention rules, CASBs help prevent unauthorized data transfers. DLP features are essential for protecting sensitive data from being leaked or misused. CASBs can classify and monitor data, applying encryption or redaction as necessary to safeguard information.
- Threat Protection: CASB offers extra security by instantly recognizing and thwarting attacks. This feature is essential for organizations that need to react quickly to potential cybersecurity incidents. With advanced threat intelligence and analytics integration, CASBs can detect and neutralize sophisticated cyber threats.
- Compliance: CASB ensures cloud usage is compliant with regulatory requirements. This feature especially benefits industries with stringent regulatory standards, such as healthcare and finance. CASBs offer comprehensive compliance reporting and auditing capabilities to help organizations meet legal obligations without operational disruptions.
- Visibility and Control: CASB provides comprehensive visibility and control over cloud applications and services. This allows businesses to implement security regulations and monitor user behavior successfully. Administrators can set policies based on user roles, locations, and device types, ensuring only authorized personnel access sensitive resources.
Real-World Applications of CASB
Many organizations have successfully implemented CASB solutions to enhance their cybersecurity frameworks. For instance, some large enterprises have utilized CASB to maintain compliance with GDPR, significantly reducing their risk of data breaches. GDPR compliance is a significant concern for many companies, and CASBs play a vital role in ensuring that data protection measures are in place.
Companies across sectors have leveraged CASB solutions to streamline security measures and improve data governance. From securing financial transactions to protecting patient records in healthcare, CASBs offer versatile solutions for various industries. In the financial sector, CASBs help control access to sensitive customer information. In contrast, in the healthcare sector, they ensure the confidentiality and integrity of patient data by fortifying electronic health record systems.
Choosing the Right CASB Solution
When choosing a CASB solution, consider scalability, ease of interface with current systems, and your company’s unique security requirements. Trusted sources like ZDNet’s Best Cloud Security Solutions list can be a good starting point for comparison. Look for CASBs that offer a seamless integration process, as complex implementations can lead to operational challenges and increased costs.
The right CASB solution should align with your organization’s goals and provide comprehensive security features. Choosing a CASB that can adjust to the changing cybersecurity scenario with solid support and frequent upgrades is also beneficial. Consider conducting a proof of concept to evaluate how the CASB performs in your environment and gather feedback from key stakeholders to ensure it meets your needs.
Future of CASB
As cloud computing continues to grow, the role of CASB in cybersecurity will only become more critical. Future advancements in CASB technology will likely improve AI-driven threat detection and enhance integration capabilities with a broader range of cloud services. AI and machine learning will enable CASBs to predict and respond to threats more accurately, offering proactive protection rather than reactive measures.
Furthermore, the evolution of CASB will be driven by the increasing need for advanced data protection and regulatory compliance across all industries. The adoption of CASB solutions is expected to rise as organizations seek more reliable and efficient ways to secure their cloud environments. Emerging trends, such as using zero-trust security models and secure access service edge (SASE) architectures, will further integrate CASB capabilities to provide holistic security solutions.
Read More: BigTechoro:Complete Tech Solution Everyone